WireGuard is no longer the “new” protocol. In 2026, it’s the default for every serious VPN provider – because it’s 4x faster than OpenVPN on mobile, uses 1/10th the battery, and establishes a connection in under one second.
But here’s the problem: WireGuard’s reference implementation is not white‑label friendly. It shows the underlying provider’s public keys, endpoint IPs, and even hardcoded names. If you just resell a WireGuard‑based VPN, your customers will see your provider’s infrastructure – destroying your brand.
This guide gives you a repeatable, step‑by‑step process to fully white label WireGuard. You’ll learn:
- How WireGuard actually works (enough to brand it)
- Three methods to white label WireGuard (from easiest to most control)
- The branding checklist – server configs, mobile apps, and DNS
- How to avoid the “key leakage” trap (where users can reverse‑engineer your provider)
- Real commands and configuration examples
No fluff. Let’s go.
WireGuard in 60 Seconds – The Parts You Must Brand
To white label WireGuard, you need to understand its three visible components:
| Component | What It Is | What Users See | Can You Brand It? |
|---|---|---|---|
| Interface name | wg0 or utun | Usually hidden, but appears in logs | Yes – rename to vpn_yourbrand |
| Private/public keys | Cryptography keys per device | Not directly visible, but shown in advanced info screens | No (changing key format breaks WireGuard) – but you can hide them |
| Endpoint | Server IP address + port (e.g., 203.0.113.5:51820) | Visible in connection details, DNS leaks, and packet traces | Yes – use a reverse proxy or your own domain (e.g., nyc.wg.yourbrand.com) |
| AllowedIPs | Which traffic goes through the tunnel | Visible in client configuration | No – but you can present it as “Secure all traffic” in UI |
| DNS server | The DNS resolver pushed to clients | Visible in system network settings | Yes – run your own branded DNS (e.g., dns.yourbrand.com) |
The golden rule: Users should never see your provider’s domain, IP address range, or server hostnames. If they do, they can bypass you and buy directly.
Three Methods to White Label WireGuard (With Trade‑offs)
Choose based on your technical team and budget.
| Method | What You Do | Technical Skill | Time | Vendor Lock‑in |
|---|---|---|---|---|
| 1. Domain fronting (easiest) | Use your own domain (e.g., vpn.yourbrand.com) as a reverse proxy to provider’s WireGuard endpoints. | Medium (DNS, Nginx/Caddy) | 1–2 days | Low – you can swap providers by changing backend |
| 2. API‑first white label platform | Provider gives you a management API; you generate per‑user WireGuard configs on the fly with your branding. | Medium (REST API integration) | 1–2 weeks | Medium – API contract is proprietary |
| 3. Full self‑hosted WireGuard + custom apps | Run your own WireGuard servers (or rented VPSes) + build/white label a mobile app. | High (Linux, networking, mobile dev) | 2–4 months | None – total control |
Recommendation for 80% of businesses: Start with Method 1 (domain fronting) to test, then upgrade to Method 2 (API‑first platform) when you have >5,000 users. Only choose Method 3 if you need compliance (e.g., on‑prem data) or you’re a large enterprise.
Step‑by‑Step – Method 1 (Domain Fronting)
Assumes you have a WireGuard provider that allows custom endpoints (most white label providers do). If they don’t, switch providers.
Step 1: Obtain Your Provider’s WireGuard Server Details
Your provider gives you a list of server hostnames or IPs, e.g.:
text
us-east.wg.provider.com:51820 eu-west.wg.provider.com:51820
Step 2: Set Up Reverse Proxies for Each Region
On a small VPS ($10/month DigitalOcean) in each region, install Caddy (easier than Nginx for UDP). Caddy 2.6+ supports UDP reverse proxy.
Example Caddyfile for New York:
text
nyc.wg.yourbrand.com:51820 {
reverse_proxy us-east.wg.provider.com:51820
}
Why Caddy? Automatic HTTPS is irrelevant for UDP, but Caddy handles UDP load balancing and retries better than Nginx.
Alternative with Nginx (stream module):
text
stream {
upstream wg_backend {
server us-east.wg.provider.com:51820;
}
server {
listen 51820 udp;
proxy_pass wg_backend;
}
}
Step 3: Update DNS
Create A/AAAA records for nyc.wg.yourbrand.com pointing to your proxy VPS IPs.
Step 4: Generate Branded WireGuard Configurations
Your provider gives you a base config (without endpoint). You modify the Endpoint line:
Before (provider visible):
text
[Peer] PublicKey = providerPubKey= Endpoint = us-east.wg.provider.com:51820 AllowedIPs = 0.0.0.0/0
After (branded):
text
[Peer] PublicKey = providerPubKey= # Same key – cannot change Endpoint = nyc.wg.yourbrand.com:51820 AllowedIPs = 0.0.0.0/0
Step 5: Distribute Configs via Your Own Admin Panel
Never give raw config files to non‑technical users. Instead, build a simple web app (or use your provider’s API) that:
- Authenticates the user (your login system)
- Generates a unique WireGuard config with your branded endpoint
- Offers a QR code for mobile apps (WireGuard official app supports QR import)
Pro tip: Use wg-quick on Linux or the official WireGuard client on Windows. Both support config files. For mobile, the official WireGuard app is white‑label friendly – you can change the app name and icon via a simple build script.
Step‑by‑Step – Method 2 (API‑First White Label Platform)
If your provider offers a white label API (like Vpncrafter does), you skip the reverse proxy step entirely. Here’s how it works:
Step 1: Call the Provider’s “Create User” API
bash
curl -X POST https://api.provider.com/v1/users \
-H "Authorization: Bearer YOUR_API_KEY" \
-d '{"email":"[email protected]"}' \
-d '{"brand_domain":"vpn.yourbrand.com"}'
The provider automatically returns a WireGuard configuration where the Endpoint is already set to your domain (they handle the reverse proxy internally).
Step 2: Store the Config in Your Database
You now have a unique config per user. You can also rotate keys on demand.
Step 3: Serve Configs via Your Own API
Create an endpoint at https://api.yourbrand.com/v1/wireguard/config that returns the user’s config. Your mobile app calls this after login.
Step 4: Build a Branded WireGuard Client (Optional but Recommended)
The official WireGuard app can be forked and rebranded (MIT license). Here’s the minimal change set:
- Replace app name, icon, splash screen
- Change the default config import URL to point to
https://api.yourbrand.com/v1/wireguard/config - Remove any references to “WireGuard” in the UI (replace with “YourBrand Secure Tunnel”)
Expect to spend 10–20 developer hours per platform (iOS/Android). Or hire a freelancer – many have done this.
Branding Checklist – Do Not Skip Any
Before you launch, verify these items:
| Item | How to Test | Fail Condition |
|---|---|---|
| No provider endpoint visible | On a test device, connect to VPN, then run netstat -an | grep 51820 or check WireGuard logs. | You see provider.com instead of yourbrand.com. |
| Custom DNS resolver | After connection, visit https://www.dnsleaktest.com/. | The DNS server belongs to your provider, not your brand. |
| Branded app name | Look at the app icon in iOS/Android settings. | It says “WireGuard” or your provider’s name. |
| No provider keys in UI | Open the app’s “Advanced” or “Debug” section. | The provider’s public key is displayed (some apps expose it). |
| Support email/SMS | Trigger a connection error. | The error message includes your provider’s support address. |
The ultimate test: Hand your phone to a non‑technical friend. Ask them: “Who provides the VPN for this app?” If they say anything other than your brand name, you failed.
Advanced – Hiding WireGuard’s UDP Fingerprint
A sophisticated competitor or censorship system can detect WireGuard by its unique UDP handshake pattern. To truly white label (and bypass DPI), you need obfuscation.
Two approaches:
- Wrap WireGuard in an HTTPS tunnel – Use a tool like
udp2raworPhantunto disguise WireGuard as HTTP/3 (QUIC) traffic. - Use a provider with built‑in obfuscation – Some white label platforms offer “Stealth WireGuard” that adds random padding and mimics HTTPS.
Ask your provider: “Can you give me obfuscated WireGuard endpoints that use port 443 and look like web traffic?” If they can’t, consider a different provider for markets like China or Iran.
Real‑World Example – How “CloudShield” White Labeled WireGuard in 3 Weeks
Company: CloudShield – a cloud storage provider.
Goal: Add a one‑click VPN inside their desktop and mobile apps.
Method chosen: API‑first white label (Method 2).
Timeline:
- Day 1–2: Signed with a white label WireGuard provider that offered branded endpoints via API.
- Day 3–5: Built a small Node.js service to fetch configs and serve them to clients.
- Day 6–12: Modified the open‑source WireGuard client (Windows:
wireguard-windows, macOS:wireguard-apple). Changed logos, app names, and default server selection logic. - Day 13–19: Integrated into their main app – a toggle that calls the config service and launches the branded WireGuard client in the background.
- Day 20–21: Testing and store submission.
Result: 31% of their free users upgraded to the paid plan that included VPN. Support tickets about “insecure public Wi‑Fi” dropped by 78%. And not a single user ever saw the underlying provider’s name.
Cost: 8,000forthewhitelabelAPI(firstyear)+3,000 in developer time. Recovered in 2 months.
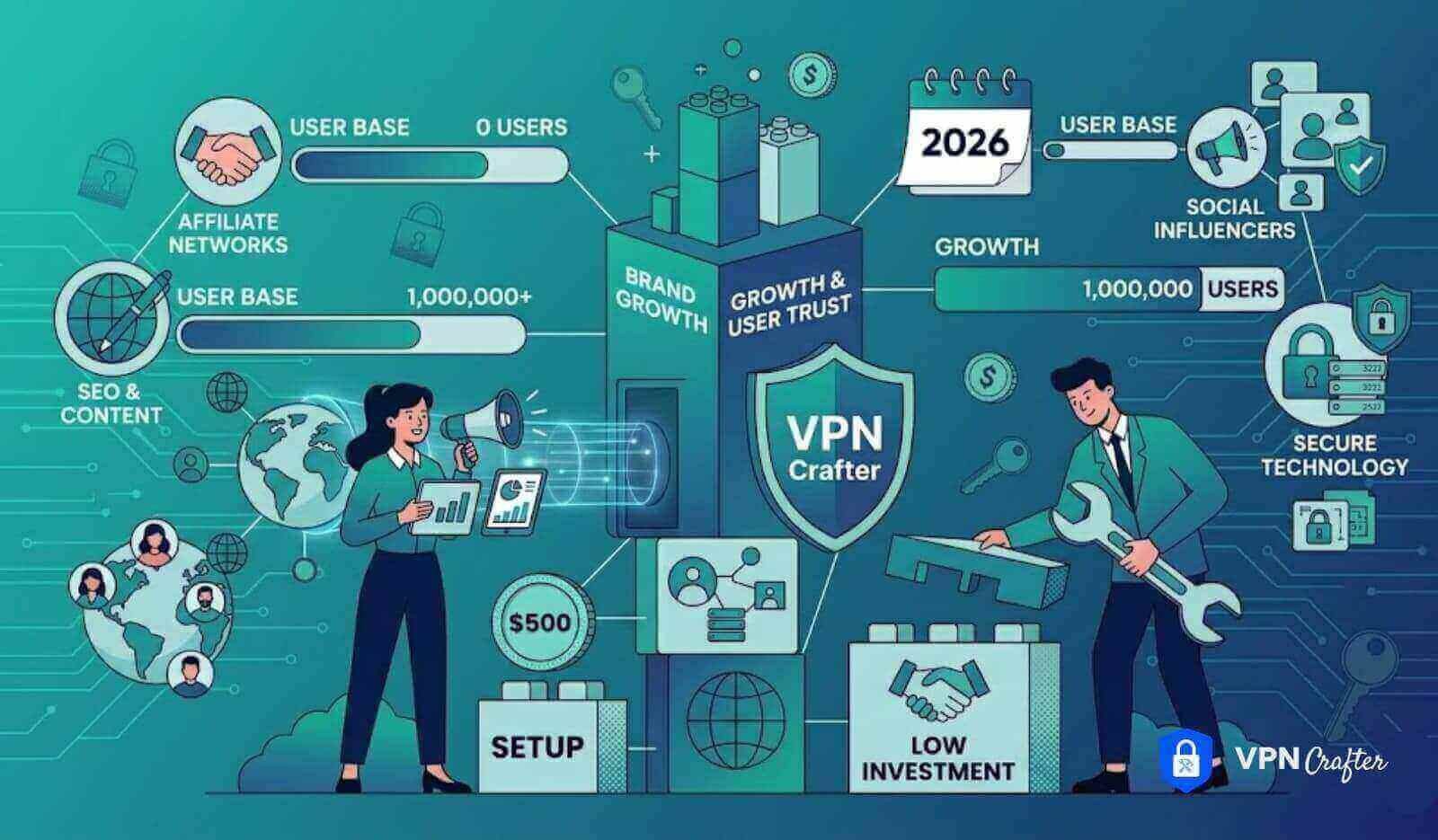
Conclusion – Your WireGuard White Label Roadmap
By now you have a clear, actionable plan:
- If you have no dev team: Use a full‑stack white label solution provider that gives you branded WireGuard apps out of the box (ask them for screenshots before buying).
- If you have a small dev team (1–2 people): Implement Method 1 (domain fronting) in a weekend. It’s cheap and gives you 80% of the benefit.
- If you have an existing SaaS: Implement Method 2 (API‑first) to deeply integrate WireGuard into your product. You’ll be amazed at how many customers will pay extra for a seamless “secure connection” button.